X-Rated Extortion
If you keep up to date with the information security news, you may be aware that opportunists are trying to extort money from unsuspecting people by threatening to leak videos of them watching X-rated content. In one example this week, one such victim shared their story of being contacted by a cybercriminal who claimed to have hacked his PC and obtained compromising webcam footage of him watching adult content.
The claim might well have horrified the victim, but here’s the important point: no such video existed.
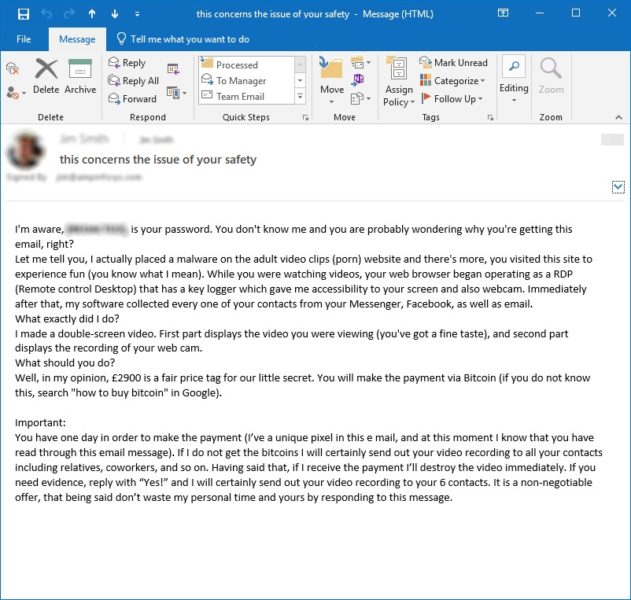
This is, in fact, a fairly common scam. In reality, all the criminal had actually managed to obtain was a weak password, extracted from a hacked website that the victim had visited some time ago. The criminal then showed the password to the victim as ‘proof’ of having carried out a much more sophisticated (but fictional) hack and let his imagination do the rest. The attacker’s email is shown below.
As Mark, our resident security expert, explains, “this sort of attack depends on the fact that users use the same password for multiple sites; they can then be tricked into believing the attacker has them cornered. Anyone who is tech savvy will no doubt question its authenticity. These cybercriminals have only really managed to hack a small-time website somewhere, and the password is, indeed, one of the low-level passwords that the victim has evidently used at some point in the past. The intrusion goes no further than that. However, if the attackers are sending these emails out to enough people, the scare factor is going to be significant enough to convince some of them to pay.
"There are numerous variants of this kind of scam, dependent upon the sort of website that has been hacked, but they tend to involve sites that have the potential to cause nuisance or embarrassment. In recent weeks, a number of North West businesses have rung us with concerns like these and we've been able to reassure them that it's no more than a scam. Nevertheless, it’s an important lesson about the importance of setting complex passwords, changing them regularly, and using a different password for every platform – even those sites where you aren't really too concerned about the security of the account.
"As a business, even the most effective security systems can't control what individual employees do in their free time. Similarly, a business can't stop a criminal from hacking an unrelated third-party website in order to gather lists of email addresses and passwords. However, businesses can certainly make employees aware of the threat, and make sure they understand the risks of using work-related email addresses for anything but professional purposes. At a practical level, companies should also install appropriate security safeguards and filters on any company-owned mobile devices that employees might take outside of the office. ”

Managed IT Security
For nearly 20 years, we’ve been helping North West businesses to stay secure and well protected in the face of a growing range of cyber threats. Offering hardware, managed IT security, advice and proactive monitoring, remote updates and more, we’ll keep your business safe in the digital world. Contact AMP today to see how we can help you fight cybercrime effectively 0800 368 7730.









